I believe in using every tool available to put your best foot forward. The thoughts and experiences on this page are my own; I use AI to help ensure grammar is accurate.
BLUF (Bottom Line Up Front)
Traditional security models focus on when an attack happens. The Diamond Model of Intrusion Analysis focuses on who, how, and where. By mapping the relationships between an adversary, their capabilities, their infrastructure, and the victim, we move beyond chasing isolated alerts to tracking entire campaigns. Using the SolarWinds (SUNBURST) breach as a roadmap, we can see how “pivoting”—using one known detail to find the rest—is the only way to defend against modern Advanced Persistent Threats (APTs).
The Blind Spot in Sequential Models
Most frameworks, like the Cyber Kill Chain, are linear. They are excellent for describing the chronology of a break-in—from Reconnaissance to Actions on Objectives—but they struggle to illustrate how incidents are logically connected.
If an attacker hits a county courthouse in Western Iowa and a school district in Des Moines using different malware but the same Command and Control (C2) server, a linear model treats them as unrelated events. The Diamond Model solves this by viewing every intrusion as an “atomic-level” element consisting of four core vertices.
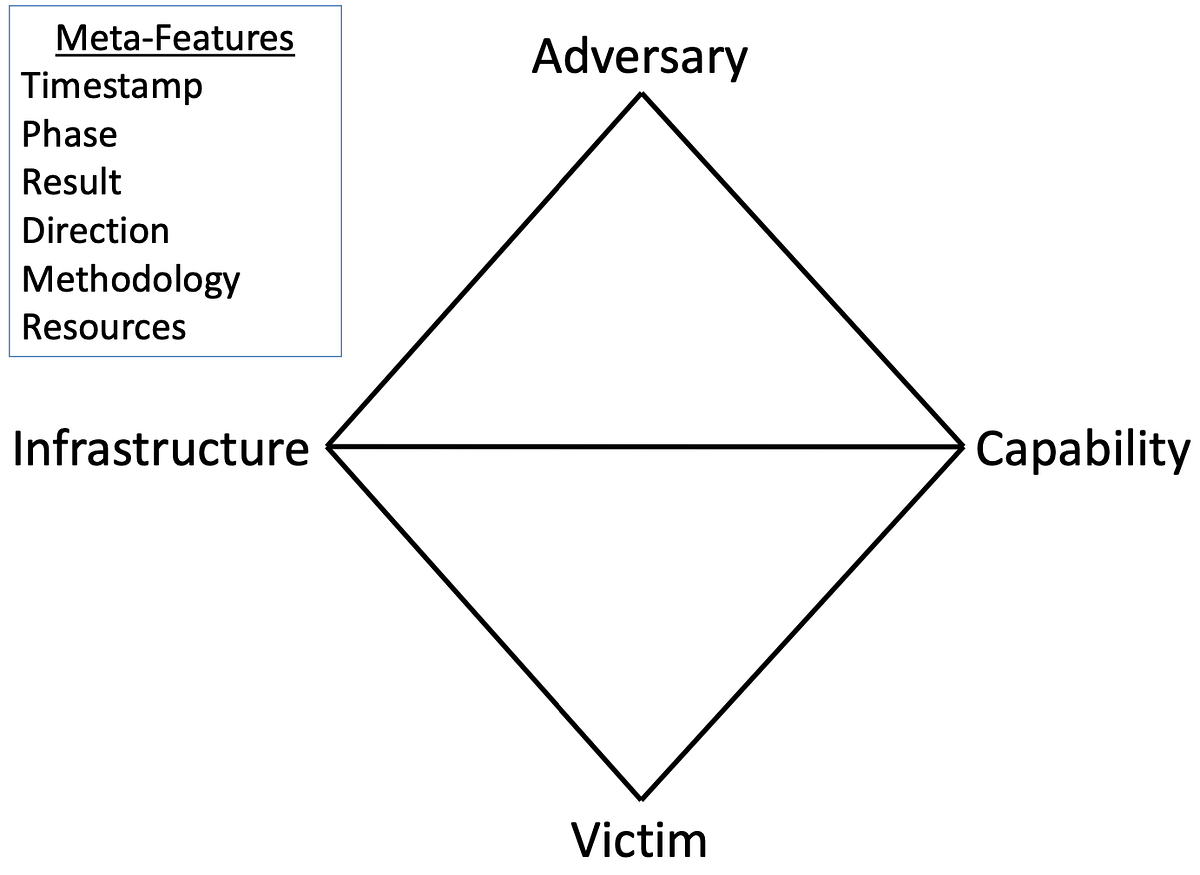
When you connect these dots, you get a diamond shape that reveals the attacker’s operational signature. By linking these “diamonds” together, we create Activity Threads. This allows an analyst to hypothesize the overall sequence of events even when data for certain phases of the attack are missing.
The Four Vertices: Broken Down
The model is built on four core features that are edge-connected, meaning a change in one often necessitates a change in the others.
- Adversary: The “Who.” This is the actor, their organization, and their intent (e.g., State-sponsored espionage vs. Cybercrime).
- Capability: The “How.” The tools and techniques used (e.g., SUNBURST malware, Golden Ticket attacks).
- Metaphor: Think of a Capability as a weapon system’s ballistic signature. Just as a forensic team can identify a specific rifle by the rifling marks on a bullet, analysts identify adversaries by the “wear patterns” in their code and the specific TTPs in their tactical loadout.
- Infrastructure: The “Where.” The physical or logical communication paths are used to maintain control.
- Metaphor: Infrastructure represents the adversary’s logistical supply lines. Establishing these lines—C2 servers, domains, and compromised jump boxes—is expensive and time-consuming. Because attackers are often resource-constrained, they “reuse” these lines. If we cut one “supply route,” we can often map the entire logistics hub.
- Victim: The “Target.” The specific asset or organization being exploited (e.g., your SQL database or an Iowa municipality’s SCADA system).
The Sub-Vertices (Meta-Features)
To get truly granular, the Diamond Model includes six Meta-Features that add necessary texture to the analysis:
- Timestamp: The start and end time of the event.
- Phase: Where this fits in the Kill Chain (e.g., Delivery vs. Installation).
- Result: Success, Failure, or Detection status.
- Direction: Victim-to-Infrastructure (Outbound) or Infrastructure-to-Victim (Inbound).
- Methodology: The class of activity (e.g., spear-phishing vs. web exploit).
- Resources: External elements required (e.g., specific libraries or hardware).
Case Study: The SolarWinds (SUNBURST) Campaign
To see the model in action, we look at the SolarWinds compromise—a massive campaign attributed to the Russian SVR (tracked as Cozy Bear or APT29).
Adversary (The “Who”)
- The Actor: APT29 / Cozy Bear.
- The Motive: Strategic, long-term espionage aimed at the U.S. Federal Government and its critical supply chains.
Capability (The “How”)
- The Tools: The primary vector was SUNBURST, a trojanized DLL injected into legitimate SolarWinds Orion updates. This gave the adversary high-level privileges in any environment where those accounts were trusted.
Infrastructure (The “Where”)
- The Communication: The malware used a specific domain,
avsvmcloud[.]com, for beaconing and command delivery. By identifying this single piece of infrastructure, defenders could “pivot” to see every other victim in the campaign.
Victim (The “Target”)
- The Reach: Roughly 18,000 organizations downloaded the poisoned update, though the adversary only selected a small subset (estimated at ~100) for follow-on exploitation.
- The Iowa Reality: Many Iowa local governments and municipal utilities use the same “enterprise-grade” management software as federal agencies. In this model, the software vendor becomes a component of the Infrastructure vertex that the adversary exploits to reach the Victim.
The Power of “Pivoting”
The Diamond Model’s real value is pivoting—using what you know to find what you don’t.
In the SolarWinds case, defenders used a known Infrastructure (the suspicious domain) to find the Capability (the SUNBURST hash). By analyzing that capability, they discovered other Victims. This forms what analysts call a “cyber frontline,” where adversary intelligence and operational defense meet.
Integrating this with the Active Cyber Defense Cycle (ACDC) allows us to use gathered intel to perform Environment Manipulation—such as changing firewall rules or modifying network architecture specifically to break the adversary’s known infrastructure.
Why This Matters for Iowa SLTTs
In rural schools and local governments (SLTTs), we don’t have a “passive” luxury. We must be proactive.
- Community Intelligence: If three Iowa counties share their “Infrastructure” findings (IPs, domains) through the MS-ISAC, they build a shared Diamond Model that protects the whole sector.
- Strategic Communication: The “Victim” vertex at the bottom of the diamond makes the business risk explicit. This helps you explain to a City Council why a specific threat to “Customer Data” or “Critical Infrastructure” warrants an immediate budget for remediation.
Key Takeaways
- Pivoting is the Superpower: Start with one indicator and use the edges of the diamond to map the rest of the campaign.
- Infrastructure is the Weak Point: Adversaries are human; they get lazy and reuse their “logistics.”
- Context Over Alerts: An alert is just noise. A Diamond Model event is a story that helps you predict the adversary’s next move.
Sources
- CISA Alert (AA20-352A): Advanced Persistent Threat Compromise of Government Agencies.
- Mandt, E. J. (2017): Integrating Cyber-Intelligence Analysis and Active Cyber-Defence Operations. Journal of Information Warfare.
- Caltagirone, S., et al. (2013): The Diamond Model of Intrusion Analysis.
Is your team tracking alerts or campaigns? Follow Nueva Guardia Cyber Consulting on LinkedIn for more strategies on defending Iowa’s critical infrastructure.
