I believe in using every tool available to put your best foot forward. The thoughts and experiences on this page are my own; I use AI to help ensure grammar is accurate.
Executive Summary
This briefing synthesizes two foundational cybersecurity frameworks—the Cyber Kill Chain and the Diamond Model of Intrusion Analysis—to provide an integrated defense framework for Iowa’s State, Local, Tribal, and Territorial (SLTT) organizations. By examining the SolarWinds (StellarParticle) campaign conducted by APT29 (Cozy Bear), this document demonstrates how technical researchers can move beyond isolated alerts to understand entire adversary campaigns.
The core takeaway is that while the Kill Chain describes the chronology of an attack, the Diamond Model illustrates the relationships between actors, their tools, and their victims. For an Iowa municipality or school district, integrating these models enables “analytic pivoting,” in which a single piece of evidence (such as a suspicious domain) can be used to uncover the adversary’s entire logistical infrastructure.
The Rural Reality of Global Threats
In December 2020, the world learned that a Russian intelligence agency (SVR) had compromised SolarWinds’ software supply chain. While this made headlines at the federal level, the impact hit home in Iowa. Your county’s HR portal, the city’s utility billing system, or the local school’s grading platform may run on servers managed by the same “enterprise-grade” tools targeted in this breach. In this environment, a small-town IT department isn’t just defending against local “script kiddies”; they are facing the same sophisticated actors that target the U.S. Federal Government.
Impact: Why Framework Integration Matters
For an organization with limited staff, traditional security often feels like a game of “whack-a-mole.”
- The Kill Chain helps you identify where to break an attack.
- The Diamond Model helps you identify who is attacking and what else they might be doing.
- Combined Impact: You stop chasing static IPs and start anticipating the adversary’s next move by understanding their “operational signature.”
Technical Analysis: The Cyber Kill Chain
The Kill Chain, developed by Lockheed Martin, identifies seven phases of an intrusion. Breaking any single link in this chain can stop the entire attack.
| Phase | Description | APT29 SolarWinds Application |
|---|---|---|
| 1. Reconnaissance | Researching targets. | Scanning for employee info, DNS records, and software versions. |
| 2. Weaponization | Building a malicious tool. | Injecting the SUNBURST backdoor into legitimate SolarWinds Orion DLL files. |
| 3. Delivery | Sending the weapon. | Distributing the poisoned update through the normal SolarWinds update process. |
| 4. Exploitation | Weapon activates. | The trojanized DLL executes. Note: SUNBURST featured a 14-day dormancy period before beaconing to evade detection. |
| 5. Installation | Establishing foothold. | Deploying secondary backdoors like TEARDROP; using WMI for persistence. |
| 6. Command & Control | Communicating with backdoor. | Beacons sent to avsvmcloud[.]com; use of steganography and HTTP for exfiltration. |
| 7. Actions on Obj. | Achieving the goal. | Stealing O365 emails and Golden SAML token forgery to bypass MFA. |

Technical Analysis: The Diamond Model
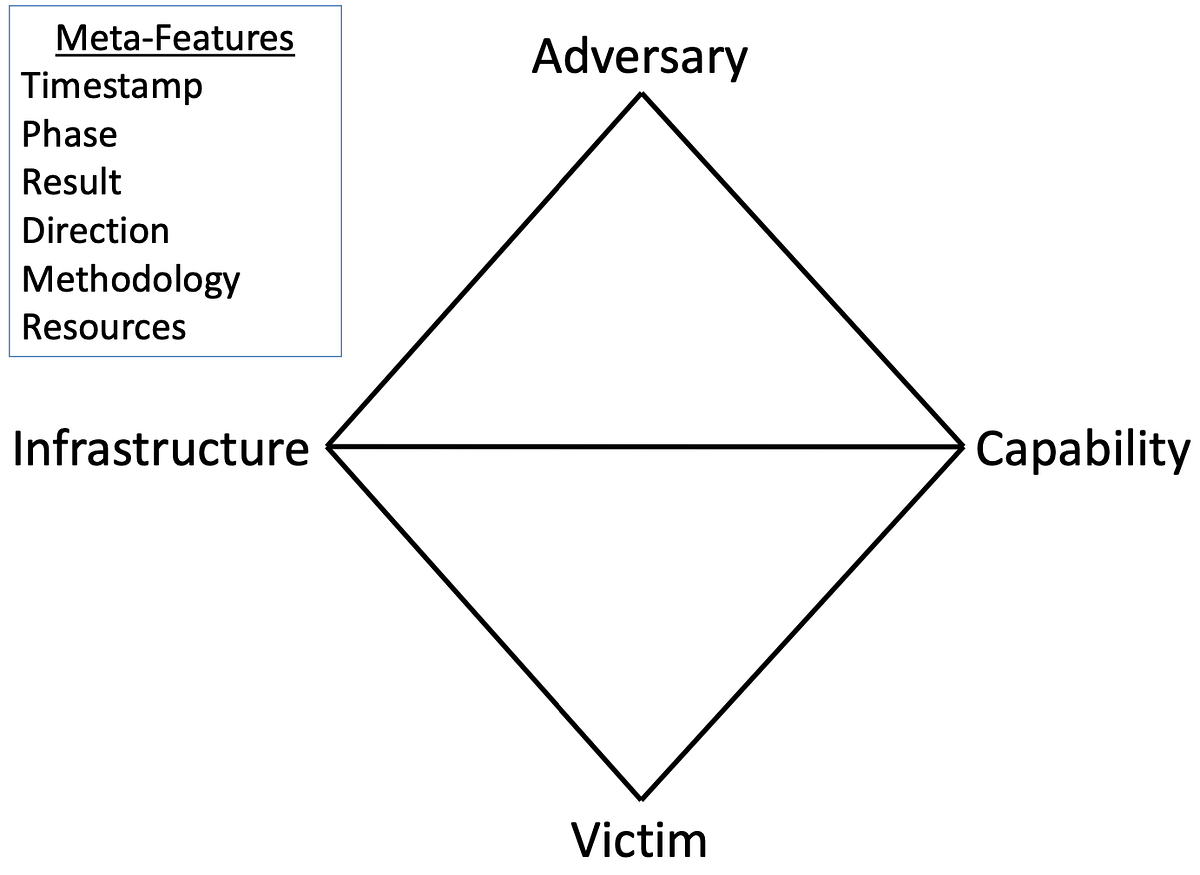
The Diamond Model focuses on the “atomic” features of an intrusion event, organized across two axes: the Social-Political Axis (Adversary-Victim) and the Technical Axis (Capability-Infrastructure).
- Adversary (The “Who”)
- Actor: APT29 (Cozy Bear / SVR).
- Motive: Strategic, long-term espionage.
- Iowa Context: Local governments are targeted not for their money, but as part of a broader mission to understand U.S. infrastructure and supply chains.
- Capability (The “How”)
- Malware: SUNBURST, SUNSPOT, TEARDROP, and GoldMax.
- Techniques: Golden SAML Token Forgery, Password Spraying, and DCSync attacks.
- Tools: Use of legitimate utilities like 7-Zip to archive stolen data.
- Infrastructure (The “Where”)
- C2 Infrastructure: Randomly generated subdomains of avsvmcloud[.]com.
- Logistical Supply Lines: Compromised OWA servers used as staging points; VPN IPs originating from the same country as the victim.
- Victim (The “Target”)
- Persona: Government, technology, and consulting organizations.
- Assets: Exchange servers, AD FS containers, and sensitive wikis.
Meta-Features: Connecting the Vertices Beyond the four vertices, the Diamond Model uses “meta-features” to provide context. For the SolarWinds breach, the Timestamp (spanning years) and Phase (connected to the Kill Chain) allow analysts to see the attack not as a single event, but as a deliberate campaign.
Strategic Synthesis: Analytic Pivoting
The true power of these models lies in Analytic Pivoting—using a known vertex to find an unknown one.
- Victim discovers malware: A school’s endpoint protection flags a suspicious DLL.
- Capability reveals Infrastructure: Analysis of the DLL reveals it “phones home” to a specific domain.
- Infrastructure reveals further Victims: Searching logs for that domain reveals other compromised machines on the network.
- IP Ownership reveals Adversary: Technical details of the C2 infrastructure link the activity to APT29’s known TTPs.
Integrating with the Active Cyber Defense Cycle (ACDC)
By synthesizing these models, Iowa IT teams can transition through the ACDC:
- Asset Identification: Knowing exactly where SolarWinds Orion is installed.
- Network Security Monitoring: Looking for the specific beaconing patterns (e.g., HTTP GET requests) associated with SUNBURST.
- Incident Response: Using tools like SANS SIFT Workstation to evaluate the environment.
- Environment Manipulation: Changing firewall rules to block known APT29 C2 domains before an infection reaches the “Actions on Objectives” phase.
Action: Steps for Iowa IT Professionals
Iowa’s rural organizations do not need enterprise-grade budgets to implement these defenses. Prioritize the following tax-funded and low-cost actions:
- Join the MS-ISAC: The Multi-State Information Sharing and Analysis Center (MS-ISAC) provides free threat feeds that include the “Infrastructure” vertices (IPs/Domains) used by APTs.
- Enforce Multi-Factor Authentication (MFA): APT29 specifically targets credentials. While they can forge tokens, basic MFA blocks the initial “password spraying” used to gain a foothold.
- Audit Service Principals and OAuth Apps: As seen in SolarWinds, APT29 adds credentials to legitimate cloud applications to maintain access. Regularly review these permissions in Azure AD/Microsoft 365.
- Practice “Principle of Least Privilege”: Limit the number of Domain Admins. APT29 uses privileged accounts to move laterally through the network.
- Utilize CISA Resources: Enroll in CISA’s Cyber Hygiene (CyHy) Services. These are free, automated vulnerability scans that provide weekly reports on your internet-facing systems—helping you patch the “Infrastructure” and “Capability” vertices before an adversary can exploit them. Use their “Known Exploited Vulnerabilities” (KEV) catalog to prioritize critical patches.
Takeaway
Focus on the “logistics” of the attack. Adversaries are human; they get lazy and reuse infrastructure. By using the Diamond Model to identify an attacker’s logistical supply lines (IPs and C2 servers) and the Kill Chain to identify their operational phase, Iowa’s SLTTs can move from reactive defense to proactive campaign intelligence.
Sources
- CISA Alert (AA20-352A): Advanced Persistent Threat Compromise of Government Agencies.
- MITRE ATT&CK: SolarWinds Compromise, Campaign C0024.
- Caltagirone, S., Pendergast, A., & Betz, C. (2013): The Diamond Model of Intrusion Analysis.
- Mandt, E. J. (2017): Integrating Cyber-Intelligence Analysis and Active Cyber-Defense Operations.
- Hutchins, E. M., et al. (2011): Intelligence-driven computer network defense informed by analysis of adversary campaigns and intrusion kill chains.
- CrowdStrike (2022): Observations from the StellarParticle Campaign.
